Bug #97930
closedHarden distribution overview in extension manager
Added by Frank Nägler over 2 years ago. Updated about 1 month ago.
100%
Description
The distribution overview page is vulnerable for XSS.
If a distribution description contains XSS within the first 150 characters, the overview execute the code.
File: EXT:extensionmanager/Resources/Private/Partials/List/Distribution.html
Affected code: {distribution.description -> f:format.crop(maxCharacters: 150) -> f:format.raw()}
Reproduce: inject the code <script>alert('XSS');</script> to the description of an extension / distribution and open the overview.
Files
| exteions.xml.gz.png (78.4 KB) exteions.xml.gz.png | Oliver Hader, 2022-07-25 11:10 |
 Updated by Oliver Hader over 2 years ago
Updated by Oliver Hader over 2 years ago
- Related to Task #82000: Use new card layout for distributions list view added
 Updated by Oliver Hader over 2 years ago
Updated by Oliver Hader over 2 years ago
Did not manage yet to test it with extensions.typo3.dev (it does not accept files).
In case description and other meta-data is passed as is via TER upload → extensions.xml → local XML import, this is a severe XSS vulnerability effecting all TYPO3 sites.
 Updated by Frank Nägler over 2 years ago
Updated by Frank Nägler over 2 years ago
I tested it by changing the data directly in the database. I guess, that there is no filter in the upload process.
 Updated by Oliver Hader over 2 years ago
Updated by Oliver Hader over 2 years ago
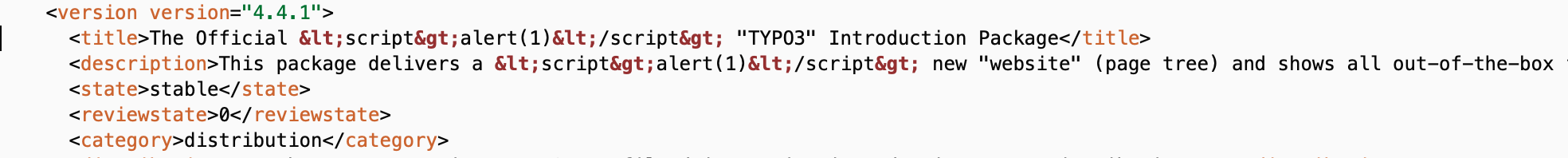
- File exteions.xml.gz.png exteions.xml.gz.png added
extenions.xml.gz contents are imported as is into the database → XSS confirmed for that part of the vector.
The missing piece is still how the TER handles/sanitizes uploaded data.
 Updated by Oliver Hader over 2 years ago
Updated by Oliver Hader over 2 years ago
- Priority changed from Should have to Must have
 Updated by Oliver Hader over 2 years ago
Updated by Oliver Hader over 2 years ago
- Target version set to Release February 2024
 Updated by Oliver Hader about 2 years ago
Updated by Oliver Hader about 2 years ago
Did not manage to exploit this via upload:
<version version="9.9.0">
<title>The Official TYPO3 Cross-Site Scripting Package</title>
<description>This package provides XSS by using scriptalert(12345)/script</description>
<state>stable</state>
<reviewstate>0</reviewstate>
<category>distribution</category>
...
<version version="9.9.1">
<title>The Official TYPO3 Cross-Site Scripting Package</title>
<description>&lt;script&gt;alert(2)&lt;/script&gt; ![CDATA[scriptalert(12345)/script &lt;script&gt;alert(3)&lt;/script&gt;]]</description>
<state>stable</state>
<reviewstate>0</reviewstate>
<category>distribution</category>
ext_emconf.phphas not been sanitized/modied- but the creation of
extensions.xmlused a corresponding sanitization,
at least since January 2017 (I did not track earlier changes in other locations), see https://git.typo3.org/services/t3o-sites/extensions.typo3.org/ter/-/blame/c755d1df7b9e7cd41d969e14bc8e66077f7c753a/html/typo3conf/ext/ter/class.tx_ter_helper.php?page=1#L527-533
 Updated by Oliver Hader about 2 years ago
Updated by Oliver Hader about 2 years ago
- Status changed from Accepted to Needs Feedback
- Priority changed from Must have to Should have
After analyzing the behavior of the actual TER, I don't see a real attack vector anymore. I'd opt for fixing this in public, what do you think?
 Updated by Frank Nägler about 2 years ago
Updated by Frank Nägler about 2 years ago
I am OK with fixing it in public.
The sanitizer looks a bit weird, I think there are better ways to handle XML or data in XML, but your test proves that no vector exists, so let's fix it public.
 Updated by Torben Hansen about 2 years ago
Updated by Torben Hansen about 2 years ago
Since the issue can not be exploited using the TER extension upload, a fix in public is also OK for me.
 Updated by Oliver Hader about 2 years ago
Updated by Oliver Hader about 2 years ago
- Target version changed from Release February 2024 to public
 Updated by Oliver Hader about 2 years ago
Updated by Oliver Hader about 2 years ago
- Project changed from 1716 to TYPO3 Core
- Subject changed from XSS in distribution overview to Harden distribution overview in extension manager
- Category changed from OW-A07: Cross Site Scripting to Security
- Target version deleted (
public) - Reporter deleted (
Frank Nägler) - Affected Version deleted (
9.0, 10, 11)
→ moved from security tracker to public core tracker
 Updated by Gerrit Code Review 4 months ago
Updated by Gerrit Code Review 4 months ago
- Status changed from Needs Feedback to Under Review
Patch set 1 for branch main of project Packages/TYPO3.CMS has been pushed to the review server.
It is available at https://review.typo3.org/c/Packages/TYPO3.CMS/+/85260
 Updated by Gerrit Code Review 4 months ago
Updated by Gerrit Code Review 4 months ago
Patch set 1 for branch 12.4 of project Packages/TYPO3.CMS has been pushed to the review server.
It is available at https://review.typo3.org/c/Packages/TYPO3.CMS/+/85203
 Updated by Georg Ringer 4 months ago
Updated by Georg Ringer 4 months ago
- Status changed from Under Review to Resolved
- % Done changed from 0 to 100
Applied in changeset b639beaea72e28ae30f0133ba035077e4dbbdbd0.
 Updated by Gerrit Code Review 4 months ago
Updated by Gerrit Code Review 4 months ago
- Status changed from Resolved to Under Review
Patch set 2 for branch 12.4 of project Packages/TYPO3.CMS has been pushed to the review server.
It is available at https://review.typo3.org/c/Packages/TYPO3.CMS/+/85203
 Updated by Georg Ringer 4 months ago
Updated by Georg Ringer 4 months ago
- Status changed from Under Review to Resolved
Applied in changeset d325006b19c1c3b16768180b7289f50ea4643567.